Proxy Log Explorer Enterprise Edition is a comprehensive application that enables you to monitor and examine how your proxy server is being used by others. It can be put together detailed reports for a wide range of events, such as visitors and bandwidth trends, site categories, file types, search engines, and unique IP addresses.
The tool supports a long list of proxy log file types, created with Microsoft Forefront Threat Management Gateway 2010, Microsoft Internet Security and Acceleration Server, Microsoft Web Proxy Server, Squid, Netscape Proxy, Youngzsoft CCProxy (including v2010), SuperLumin Networks Nemesis, and others (WC3).
It's capable of extracting compressed log files (e.g. BZIP2, GZIP, RAR, ARJ, 7Z, LHA, LZMA) and of downloading them from various sources, namely local drives, network locations, the web, FTP, or databases via ODBC.
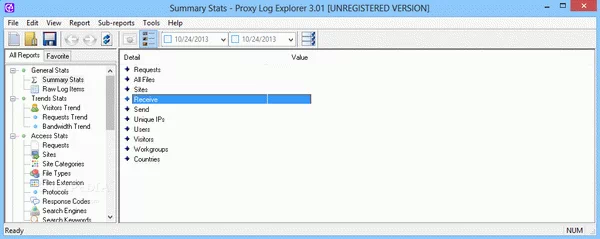
Proxy Log Explorer Enterprise Edition is wrapped in a pro-grade, yet user-friendly interface, where you can get started by specifying the locations with log files. The program auto-scans the supported log files and loads them in the database.
From this point on, you can visit all compiled reports when it comes to general statistics (summary, raw log items), trends (visitors, requests, bandwidth), access (requests, sites, site categories, file types and extensions, protocols, response codes, search engines and keywords), visitors (unique IP addresses, users, visitors, workgroups), destination (IPs, countries, regions, cities, continents), environment (operating system, OS versions, browsers and versions, user agents), and activity (by hour of day, day of week, daily, weekly, monthly, yearly, yearly and monthly).
Information and charts can be copied or exported to HTML, MHTML, text or CSV format. It's possible to filter data by consulting a calendar, save the workspace to resume it later, use a search tool, mark items as favorites for quick access, view subreports with additional information, and update auxiliary databases in Proxy Log Explorer Enterprise Edition.
As far as program settings are concerned, you can create filters by IP, login name, request, site, response code or proxy cache, put together workgroups, disable multi-threaded processing, as well as reconfigure the associated file types when it comes to documents, video, audio, downloads, and images.
It used low CPU and low-to-moderate RAM in our tests, and carried out log scans in reasonable time. Taking into account its approachable interface and rich features, Proxy Log Explorer Enterprise Edition should meet the requirements of many business environments looking to analyze logs.
For less features, you can check out Proxy Log Explorer Professional Edition or Proxy Log Explorer Standard Edition.


Related Comments
Luciano
cheers, thanksfelipe
thanks for Proxy Log Explorer Enterprise Edition serial